As technology advances, there has been a significant increase in the need for more efficient storage systems for modern computing. That’s where Internet Small Computer System Interface (iSCSI) and Storage Networking come in handy. In this article, we’ll delve deeper into the definition of iSCSI, its functionality, and how it differs from traditional storage systems. Additionally, we will provide a brief overview of Storage Networking, including its advantages and uses in modern computing.
Internet Small Computer System Interface (iSCSI) is a storage networking protocol for transmitting data over Internet Protocol (IP) networks. In simpler terms, iSCSI is a way to send and receive storage-based data over the internet. One of the critical advantages of iSCSI is that it allows organizations to run their storage networks on their existing Ethernet infrastructures, thereby reducing costs and simplifying management.
In a traditional storage setup, data is sent and received via physical cables from the servers to the storage devices. With iSCSI, the physical wires are replaced with a network connection for storage transmission. This connection can be made over a vast area network (WAN), local area network (LAN), or the internet, allowing for remote storage across multiple locations. With iSCSI, computers can access a shared pool of storage and access data as if it were a local storage device.
One significant difference between iSCSI and traditional storage is how data is transmitted. With conventional storage systems, data is sent and received via physical cables. However, with iSCSI, data is transmitted over a network connection. This means multiple servers can access a shared data pool, making it easier for businesses to manage their storage systems. Additionally, iSCSI offers a lower cost option than traditional storage solutions such as Fibre Channel, offering more flexibility in network topology.
Storage networking involves connecting storage devices to a network for shared access among multiple servers. These networks use protocols such as iSCSI, Network Attached Storage (NAS), and Fibre Channel (FC) to transmit data from storage devices to servers. One key advantage of storage networking is that it provides a centralized storage resource that can be accessed and managed from multiple locations. Additionally, it allows for more efficient storage allocation and management across multiple servers.
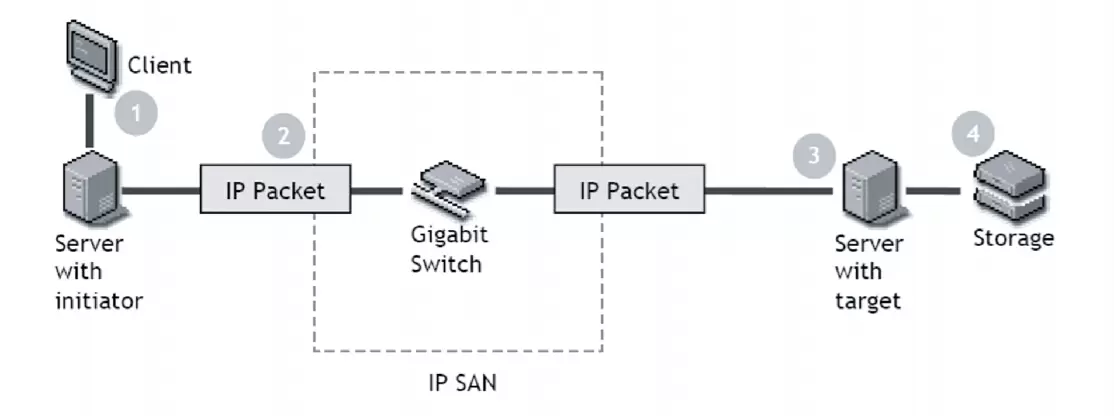
The iSCSI initiator is a software component that runs on a server or other device that needs to access storage over a network. Its primary function is to initiate Communication with an iSCSI target, establish a connection, and send SCSI commands over the web. The initiator contains the iSCSI protocol that encapsulates SCSI commands and data, enabling them to be sent over a TCP/IP network.
When a server sends a request over the network to access storage, the iSCSI initiator processes the request and sends the necessary SCSI commands to the iSCSI target. The initiator acts as the client in the iSCSI connection and is responsible for handling all the Communication between the server and the target.
An iSCSI target is a storage device or logical unit that provides block-level access to storage over a network using the iSCSI protocol. It receives SCSI commands and data from the initiator and processes them according to the command type. An iSCSI target can be a standalone storage device or a logical unit within a storage array.
The target provides storage resources to the initiator by exposing virtual volumes or logical units over the network. The initiator can access these resources as local storage devices attached to the server. The target also manages the storage resources and controls access based on authorization policies.
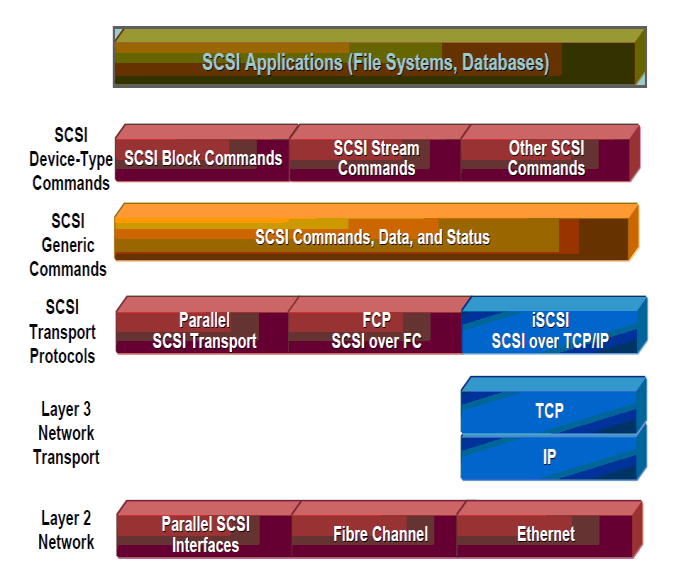
The Ccommunicated between iSCSI initiators and targets over a TCP/IP network using the iSCSI protocol. The protocol enables the encapsulation of SCSI commands and data into TCP/IP packets transmitted over the network.
The iSCSI connection is established using a three-way handshake mechanism. During the connection establishment, the initiator and target negotiate session parameters such as authentication, data transfer size, and error recovery. Once the connection is established, the initiator can send SCSI commands to the target, and the target can respond to them with status information or data transfer requests.
| Parameter | Specification |
|---|---|
| Form Factor | QSFP28 (Quad Small Form-factor Pluggable 28) |
| Data Rate | 4 × 25Gbps NRZ, total 100Gbps |
| Wavelengths | 1271nm, 1291nm, 1311nm, 1331nm (±6.5nm) |
| Optical Fiber Type | Single-mode fiber (SMF) |
| Transmission Distance | Up to 2 km (with FEC) |
| Transmitter Type | Uncooled DFB laser (DML) |
| Receiver Type | PIN photodiode |
| Power Consumption | ≤ 3.5W |
| Compliance | CWDM4 MSA, IEEE 802.3bm, RoHS |
| Connector Type | Duplex LC |
| Digital Diagnostics | Supported, via I²C (DDM/DOM) |
One key difference between iSCSI and Fibre Channel lies in their transmission technologies. iSCSI transmits data over Ethernet, the widely adopted networking standard, while Fibre Channel uses a fiber optic architecture on a dedicated network. Consequently, Fibre Channel offers higher performance with its high-speed bandwidth and superior buffering capabilities, while iSCSI can provide more flexible connection support and broader compatibility with existing Ethernet infrastructure.
Another significant difference between iSCSI and Fibre Channel is their cost-effectiveness. iSCSI is more affordable than Fibre Channel because it uses standard Ethernet networking hardware. In contrast, Fibre Channel requires specialized hardware and dedicated network infrastructure, leading to higher deployment and management costs. However, Fibre Channel offers better performance, reliability, and security features, making it more suitable for high-demand and critical applications.
iSCSI has several advantages over Fibre Channel, making it a flexible and more efficient SAN option. First, iSCSI easily integrates into existing Ethernet infrastructure, and system administrators can leverage familiar networking tools and techniques when managing their iSCSI SAN. Second, iSCSI is compatible with various operating systems, supporting almost all enterprise platforms, including Linux, Unix, and Windows. Third, iSCSI delivers high-speed data transmission over a standard, cost-effective Ethernet network, offering a cost-effective alternative to Fibre Channel.
Despite these benefits, iSCSI also presents some challenges. One significant challenge of iSCSI is its security. iSCSI uses the TCP/IP protocol, which is vulnerable to attacks such as sniffing, spoofing, and data theft. As a result, iSCSI SAN administrators need to employ advanced security measures, such as authentication, encryption, and access control, to secure their network. Another challenge of iSCSI is its performance, which may suffer from congestion and network latency, especially when dealing with high-workload applications or data-intensive workloads.
Setting up an iSCSI SAN in your network requires a few essential hardware and software components. You first need an iSCSI-capable host, such as a server or network-attached storage (NAS) device. You will also need iSCSI block storage systems, which can be storage arrays or disk enclosures. These systems will store your data and provide connections to the iSCSI host.
Once you have all the necessary hardware components, you need to follow a few critical steps to configure your iSCSI host and block storage systems. Firstly, you need to configure the iSCSI host’s network settings and ensure it has access to the iSCSI block storage systems. Secondly, you must configure the block storage systems, including creating iSCSI targets and specifying the access rights for each initiator. Finally, you must ensure the iSCSI host can communicate with the block storage systems by performing a quick connectivity test.
An iSCSI host is a device that sends SCSI (Small Computer System Interface) commands over IP networks to iSCSI targets. The host can be any device that supports iSCSI initiators or software components allowing servers to connect to iSCSI targets. Once connected to an iSCSI target, the host can access the storage devices behind it.
On the other hand, block storage systems are data storage systems that store data in blocks and present it as hard disks to the iSCSI host. With iSCSI, you can use various block storage systems, such as iSCSI storage arrays or disk enclosures. A storage array is a centralized system with multiple disk drives and can provide various forms of redundancy, ensuring that your data is always available even if individual disks fail.

Implementing iSCSI Storage Systems in a server network improves server efficiency. Firstly, iSCSI storage allows for centralized management, enabling administrators to manage all disks from a single location, streamlining the management process. Secondly, iSCSI storage systems provide better performance by reducing data access time, which leads to faster data transfer rates. Thirdly, iSCSI storage solutions improve server speed by allowing applications to share the physical disk space.
The benefits of iSCSI storage systems are not limited to improved server efficiency, as they also offer significant cost benefits. iSCSI storage solutions can save organizations money by lowering the total cost of ownership (TCO). iSCSI storage systems use standard Ethernet cabling, less expensive than proprietary hardware. This lowers the cost of deployment significantly. Additionally, iSCSI storage systems require less space and power than traditional ones, reducing operational costs.
There are potential challenges that may arise while implementing iSCSI storage systems. One of the major concerns is security. As iSCSI storage systems transmit data over TCP/IP networks, they are vulnerable to malware and hacking. Consequently, organizations must ensure that their iSCSI storage systems are secure and implement proper security measures to prevent data loss or theft. Another concern is performance optimization. While iSCSI storage systems offer better performance than traditional storage systems, organizations may need to optimize applications to take advantage of this improved performance.
In summary, iSCSI is a highly effective and affordable technology that offers many advantages over other storage systems. Its scalability, flexibility, and ease of deployment make it an ideal choice for start-ups, small businesses, and larger enterprises. By utilizing iSCSI technology, companies can experience cost savings, increased security, and more accessible storage and backup solutions maintenance.
iSCSI stands for Internet Small Computer System Interface, a storage networking protocol that enables the transmission of SCSI commands over IP networks. iSCSI is a block-level protocol allowing direct access to storage device data blocks. Its primary advantage is that it allows businesses to use their existing Ethernet infrastructure to connect servers to storage devices, which makes it easier and more cost-effective to deploy and maintain storage systems.
iSCSI has many advantages over other storage system technologies, including its scalability, affordability, and flexibility. It is scalable because it enables businesses to add more storage capacity as needed without replacing hardware or reconfiguring the network. Additionally, it is more affordable than other storage system technologies because it uses existing Ethernet infrastructure, eliminating the need for expensive Fibre Channel switches and adapters. iSCSI is also flexible, meaning it can work with various storage devices from multiple vendors, which reduces vendor lock-in.
To work efficiently and securely, iSCSI requires a reliable Ethernet network, suitable storage devices, and specialized iSCSI software. The Ethernet network must be fast and have low latency to ensure high-quality performance. Additionally, storage devices must be compatible with iSCSI and have sufficient storage capacity to meet business needs. Finally, specialized iSCSI software must be installed on both the server and the storage device to enable the transmission of SCSI commands.
Many businesses have successfully implemented iSCSI technology to improve their storage and backup solutions. For example, an Internet service provider in Singapore used iSCSI to provide its customers affordable and scalable storage solutions. With iSCSI, the provider could quickly and easily create new storage volumes on demand, making it more agile and responsive to customer needs. Additionally, a large healthcare provider in the United States used iSCSI to create a more robust disaster recovery plan. With iSCSI, the provider could replicate data between multiple sites, ensuring that critical patient information was always available in the event of a disaster.
A: iSCSI stands for internet small computer system interface. It is a storage networking standard that allows block-level access to storage devices over a TCP/IP network.
A: iSCSI works by encapsulating SCSI commands into IP packets and transmitting them over a TCP/IP network. The packets are then disassembled at the receiving end, and the storage target executes the SCSI commands.
A: There are several benefits of using iSCSI:
A: An iSCSI initiator is a software or hardware component that initiates and manages iSCSI sessions with storage targets. It allows servers to access storage resources over the network.
A: An iSCSI target is a storage server or device that provides storage resources to iSCSI initiators. It receives and executes SCSI commands sent by the initiators and delivers the requested data back over the network.
A: To connect an iSCSI initiator to an iSCSI target, you need to configure the iSCSI Initiator software on the initiator, provide the IP address or iSCSI Qualified Name (IQN) of the target, and establish an iSCSI session between the two.
A: Yes, iSCSI can utilize existing Ethernet infrastructure for storage networking. It uses standard Ethernet ports and TCP/IP protocols for Communication.
A: To use iSCSI, you will need iSCSI host bus adapters (HBAs) or iSCSI offload engines on the servers and storage targets. These specialized hardware components offload the processing of iSCSI commands from the server’s CPU, improving performance.
A: ISCSI can be used alongside other storage technologies like Fibre Channel or NAS. It provides a flexible, cost-effective solution for connecting servers to storage resources in a heterogeneous environment.
A: The main difference between iSCSI and Fibre Channel is the underlying technology and cost. iSCSI utilizes standard Ethernet infrastructure and TCP/IP protocols, making it more affordable and easier to implement. On the other hand, Fibre Channel uses dedicated, high-speed networks and specialized HBAs, making it more expensive but providing higher performance.