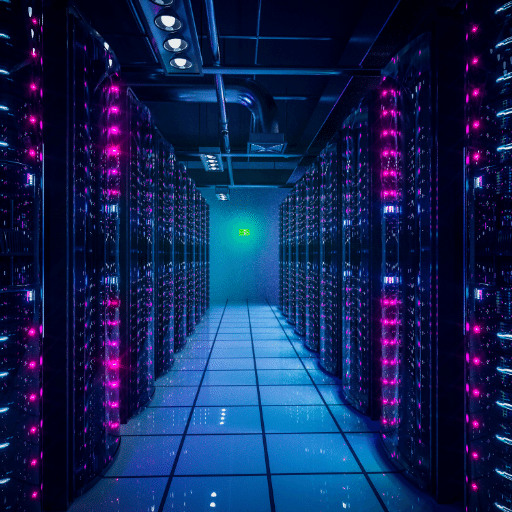
In a period where data is crucial for any organization, to protect data centers is a necessity. This blog seeks to give an all-encompassing view of the various approaches that need to be taken in order to ensure that the data center infrastructure is well protected. From physical security measures to sophisticated cybersecurity methods, every component has its own responsibility in guaranteeing the integrity, accessibility and secrecy of confidential records. As variation on cyber threats persists; it is indispensable for companies to embrace holistic strategies for safeguarding their data centers. In this article, we will look at some key ingredients as well as best practices which can help guard your data centre against possible attacks or vulnerabilities.
In today’s digital space, the rate and complexity of cyber-attacks and data breaches have reached an unparalleled level. They lure on diverse ploys such as phishing and malware to advanced persistent threats (APTs) or ransomware that targets vulnerabilities in the data center infrastructures. Not only does a successful attack lead to financial losses, but it also damages reputation and creates legal liabilities. Therefore, securing a data center is not just a mere addition; it is mandatory. This will help them minimize risks, maintain operational continuity, and secure sensitive information from unauthorized access or malicious activities.
Safeguarding Sensitive Data is important for businesses since it contains customer details, corporate finances, intellectual property rights, and proprietary business strategies. The consequences are severe if such data leaks out, hence making its protection a priority, including regulatory fines and loss of faith by customers in their brand names, hence getting low market share. From my experience as an industry expert in this area, I can affirm that dealing with various modern cyber threats requires several security layers that any organization should set up. Such a strategy would include technical controls like encryption codes and fire wall penetration detectors together with instilling in employees the culture of being secure and cautious when using the company’s systems, among other things. Also essential is comprehensive data governance and periodic security checks to identify and mitigate potential vulnerabilities beforehand. Thus organizations prioritize insulating sensitive information from potential adversaries as they aim to stay compliant with the prevailing statutes while at the same time trying to gain competitive advantage alongside boosting stakeholder trust in a more interconnected digital environment than ever before .
Compliance with regulatory security requirements is an integral part of contemporary data security initiatives. Many different laws apply to organizations including GDPR, HIPAA or CCPA which impose certain obligations for safeguarding sensitive data. My position as an expert in this area of cyber security requires me to ensure that the data protection protocols are aligned with these regulatory frameworks. This may entail carrying out thorough risk assessments, implementing necessary controls and keeping detailed records of compliance actions taken. In addition, regular compliance checks and employee training sessions are vital in order to address the constantly changing legal requirements as well as gaps that may exist. Therefore by strictly following these standards a company can escape huge fines, prevent situations when data is lost and preserve client trust thus creating a firm basis for safe operation on digital age.
Implementing comprehensive network security protocols is a series of important steps that need to be taken to ensure the integrity of the data center. First and foremost, establishing a multi-layered defense strategy is imperative, incorporating firewalls, intrusion detection systems (IDS), and intrusion prevention systems (IPS) to bolster network defenses. Also, it is essential in mitigating unauthorized access risks that robust encryption methods for data in transit and at rest are employed. Additionally, another significant strategy is network segmentation which isolates sensitive data and minimizes points of attack. Regular vulnerability assessments and penetration testing help identify and rectify potential security gaps proactively. Moreover, only authorized individuals can have access to these critical resources by having strict access controls including multi-factor authentication (MFA) and role-based access control (RBAC). Finally, maintaining updated security patches as well as continuously monitoring network traffic for any abnormal behavior are practices that strengthen network security which prevents threats.
establishing strict physical security controls is paramount to ensuring the comprehensive protection of a data center. The following are some key measures:
These physical security measures, when implemented effectively, play an integral role in safeguarding a data center’s infrastructure from unauthorized access and potential threats.
Ensuring the security and protection of data within a data center involves a multifaceted approach that addresses various potential vulnerabilities. Some key strategies include:
Critical data assets can be protected and cyber threats and unauthorized admittance prevented by implementing the above mentioned strategies for data security and protection thereby ensuring their integrity as well as confidentiality of organizations’ information systems.

To stop unauthorized interference in the data center, it is vital to deploy security officers and surveillance. This is because they provide a physical barrier against potential intruders as well respond immediately to any kind of breach of security. To ensure the data center has constant monitoring of entry points and sensitive areas, surveillance systems such as CCTV cameras are also employed. The systems help detect suspicious activities and can be linked with access control devices to give real time alerts. Thus, both security guards and surveillance become a strong security framework that ensures only authorized personnel enter into sensitive areas thereby enhancing physical security stature of the entire data center.
Planning for a safe design entails strategic planning aimed at reducing dangers by including robust measures meant for mitigating possible risks when designing a secure layout for the data centre.
These elements, when combined within the design of a data center, will greatly diminish the risk of physical security breaches while maintaining continuous protection for sensitive information located within the facility.

The integration of advanced firewall technologies plays a pivotal role in fortifying data centers against cyber threats. Modern firewalls, which go beyond traditional packet filtering, incorporate features such as Deep Packet Inspection (DPI), Intrusion Prevention Systems (IPS), and application layer filtering. These capabilities enable the identification and mitigation of sophisticated attack vectors, including malware, Distributed Denial of Service (DDoS) attacks, and zero-day exploits. Furthermore, Next-Generation Firewalls (NGFW) offer granular control over network traffic through user-aware and application-aware policies, ensuring that only legitimate and authorized communications occur within the data center environment. Employing these advanced firewall solutions provides an indispensable layer of defense, enhancing the data center’s overall security posture and safeguarding critical assets against an evolving spectrum of cyber threats.
Virtual security measures like virtual private networks (VPNs), virtual firewalls, software-defined perimeter solutions are integral parts of comprehensive protection mechanisms in a data center. These technologies abstract away from physical hardware by separating security functions which enhance scalability and flexibility. Virtual Private Networks secure remote connections over public networks through encrypted communication channels ensuring data confidentiality and integrity. Virtual firewalls serve the same purpose as their physical counterparts but they can also be integrated seamlessly into virtualized environments facilitating dynamic policy enforcement across different virtual machines(VMS).
SDP solutions further enhance security by establishing a zero-trust architecture requiring stringent authentication before granting access to network resources. This approach reduces the attack surface by making sensitive assets invisible to unauthorized users. Moreover, employing micro-segmentation techniques helps isolate workloads and limit lateral movement in case of a breach. By leveraging these virtual security measures, data centers can achieve robust multi-layered defense mechanisms while still maintaining strict compliance standards with evolving technological landscapes.
Encryption is essential for protecting data confidentiality even if it falls into the wrong hands. Advanced encryption methods such as Advanced Encryption Standard (AES) and RSA cryptography provide robust security frameworks for protecting data both at rest and in transit. AES being a symmetric encryption standard is widely adopted due to its high performance and strong resistance to attacks. On the other hand, RSA uses asymmetric key cryptography with a pair of public and private keys for secure data exchange which is ideal for safeguarding communications and digital signatures.
In addition to these foundational encryption techniques, implementing Transport Layer Security (TLS) protocols ensures secure communication channels over networks, preventing unauthorized access and data tampering. Disk encryption tools like BitLocker and VeraCrypt offer full-disk encryption protecting data stored on physical or virtual drives. By integrating these sophisticated encryption methods into their security strategies, organizations can fortify the protection of their applications and data, meeting rigorous compliance requirements and mitigating the risk of data breaches in an increasingly complex threat landscape.

To adapt to cloud security challenges, comprehensive and dynamic approaches are necessary to address the vulnerabilities that come with the use of cloud environments. Traditional data centers differ from public cloud platforms in that these ones are characterized by shared resources, multi-tenant infrastructures and remote access hence demanding advanced security measures.Firstly, strict access controls must be put in place using an identity and access management (IAM) solution which ensures that only authorized individuals can access valuable assets.
Secondly, continuous monitoring and logging is critical in real-time detection and response to potential security incidents. Amongst the solutions available include Security Information and Event Management (SIEM), a technology that aggregates log data and analyzes it for actionable insights towards faster incident response. Additionally, there should be encryption of data at rest as well as in transit so as to enhance its safety against unauthorized usage.
Thirdly, regular security assessments including vulnerability scanning and penetration testing are vital for identifying any potential weaknesses present within the cloud infrastructure. Also, they should exploit automated compliance tools for meeting industry standards and regulations.
Lastly, this requires cultivating a culture of awareness about information security through training programs all employees on a routine basis. Organizations can effectively reduce risks associated with the use of cloud environments by prioritizing these adaptive security measures thus enabling them protect their information assets more effectively.
Compliance with cyber protection requirements regarding data centers located on clouds requires organizations to employ several strategies simultaneously. Begin with enforcing stringent principles of least privilege using identity and access management (IAM) tools. Next, integrate continuous monitoring systems like Security Information Event Management (SIEM) solutions into your network so that you will be able detect any threats immediately after they occur. Also enforce encryption of data while it is being transported or when it is at rest so as to protect sensitive information. Carried out regularly more specifically vulnerability scanning and penetration testing are essential in the cloud infrastructure to identify and mitigate potential weaknesses. The use of automated compliance tools can help enterprises meet industry standards and regulatory requirements. Finally, organizations can create a security-aware culture through training programs that aim at raising consciousness among all employees. This overall strategy will ensure strong protection and compliance within cloud-based data centers.
Conducting a comprehensive assessment of safety risks is one way of recognizing weaknesses that can be preyed upon by attackers. The first step here is to conduct an asset inventory to know what needs protection, such as hardware, software and data. Secondly, threats modeling helps you determine possible attack scenarios for each asset. Next, use vulnerability scanning tools that will detect known weaknesses in the environment and complement them with penetration testing aimed at simulating real-world attacks. The last step is based on prioritizing the threats found taking into account the most probable impact and ease with which they can be exploited. Finally, review and analyze past security incidents which will help reveal common vulnerabilities and attack vectors. Document everything neatly so as to inform mitigation strategies while also building stronger security controls hence being proactive about this data center.
For developing a flexible and adaptive security strategy we need regular evaluation and adaptation to emerging threats and changing environments. Let’s start it all by setting baseline security posture through continuous risk assessments and audits so that potential vulnerabilities are always up-to-date (Washburn et al., 2016). It is important to embrace layer security approach that embeds multiple defence mechanisms like firewalls, intrusion detection systems (IDS), end-point protection among others hence creating strong defensive framework.
Implement real-time monitoring and incident response protocols to swiftly detect
and mitigate threats. Automated threat intelligence together with analytic tools improves the breadth of detection capabilities while providing timely insights into potential incidents (Fox & Doerr, 2017). Regularly update systems since this allows addressing known cases of vulnerabilities hence automated patch management should be adopted for effectiveness.
Ensure full employee training programs aimed at proactively nurturing the workforce in terms of security culture thus enhancing awareness of cyber-security best practices at all organization levels. Perform regular drills as well as simulations meant for testing the effectiveness of your incident response plans while also ensuring that you are always ready for any eventualities. Foster cooperation with other industry players so as to learn from them and be aware of the latest threats as well as mitigation techniques.
Incorporate a feedback loop to review and refine the security strategy continually. On a regular basis, update policies as well as procedures which are grounded on lessons learned from past incidents together with new threat intelligence (Fox & Doerr, 2017). This cyclic process of assessment, implementation and refinement will create a dynamic and responsive security strategy that will ensure long term resilience of the data center.
Continuous monitoring and detection systems are key aspects of any effective cybersecurity strategy. They enable organizations to identify quickly any deviations, unauthorized activities or possible threats thereby facilitating prompt response aimed at reducing risks associated with such vulnerabilities. Deployment of security information event management (SIEM) solutions is one way to achieve continuous monitoring however these should be combined with network traffic analysis tools and endpoint detection response (EDR) technologies among others. SIEM solutions provide wide-ranging visibility into the network environment by aggregating and analyzing log data from diverse sources. Network traffic analysis tools help in detecting unusual patterns or behaviors which could indicate intrusions or attempts at exfiltrating data. EDR tools give real-time monitoring on end points thereby making it easier to detect threats at device level.
Additionally, integrate machine learning and artificial intelligence to enhance detection capabilities. These advanced technologies can identify sophisticated cyber threats that traditional methods might miss by recognizing patterns and anomalies indicative of malicious activity. Establish baselines for normal network behavior using these tools, then continuously compare real-time data against baselines identifying deviations that may indicate security events.
To wrap it up, it is important to remember that continuous monitoring systems need regular calibration and updates for adaptability when there are emerging threats. Moreover, they should be audited routinely and assessed for their effectiveness before incorporating the findings into ameliorating monitoring abilities. This can be achieved through maintaining strong continuous monitoring and detection systems by organizations, thus improving their security postures and preparedness towards cyber threats in a significant manner.

A: Modern data centers’ security relies on a combination of sophisticated security tools, strict security policy and the enforcement of security standards to protect data and effectively manage operations of the data center. This covers both physical and virtual measures to guard against cloud data versus on-premises.
A: In terms of network protection of a data center, firewalls perform a critical function. They prevent unwanted traffic by creating an impenetrable barrier that only permits predetermined authorized outgoing or incoming packets. Consequently, they block unauthorized access to the information while at the same time defending against other forms of threats.
A: Key security requirements for data centers include establishing proper security policies that are comprehensive all through the entire resources in the facility and meeting certain safety criteria regarding them. Moreover, it is vital to continually update solutions aimed at countering evolving threats with regard to such IT installations as servers, networking equipment and storage devices certainly.
A: Physical Security Measures – Those put in place should comprise surveillance cameras around sensitive areas like server rooms, guards manning various entry points as well as environmental control mechanisms meant to deter unauthorized access attempts or natural calamities from occurring. These measures help ensure that intrusion does not occur on either the computer hardware or software level leading to loss of physical information stores.
A: However simple this may sound; keeping current with such services can save one from new kinds of cybercrimes we have never heard about before today thus facilitating prevention instead. Upgrading regularly makes sure that recent features are included within such facilities thus enabling them become more effective at protecting their repositories from cyber threats and hacking attempts thereby maintaining actual data integrity.
A: The importance of data center tiers is that they determine how much redundancy and fault tolerance a data center must have. Data centers with higher-tier rankings (Tiers III and IV) tend to have more comprehensive security measures against data loss and for uninterrupted operations of data centers, conforming to stricter rules regarding safety.
A: Security Services improve security within a given data center by offering customized protection systems as well as professional advice. Often these services encompass among other things deployment of guards, use sophisticated tooling, and carrying out regular audits and assessments. Security services cater to distinct requirements specific to an organization’s data center, ensuring that various forms of dangers are minimally posed.
A: Several approaches, including beefing up surveillance systems, strengthening access control mechanisms, installing physical barriers, and instituting strict visitor management protocols, may be used to make physical data centres more secure. Furthermore, it is necessary to regularly update these measures and train the team responsible for them so that the facilities remain safe from physical attacks.